AN Level 4 is Like Putting a Man on the Moon. It’s not just a Target. It’s a Strategy
In the the last month or so 8 different carriers, from a variety of places around the planet, have reached out to us to discuss
Yesterday’s post discussed the merits of front-loading effort on knowledge transfer of new starters and automated testing, whilst acknowledging the challenges that often prevent that from happening.
Today we look at the front-loading benefits of building OSS / network auto-discovery tools.
We all know that OSS are only as good as the data we seed them with. As the old saying goes, garbage in, garbage out.
Assurance / network-health data is generally collected directly from the network in near real time, typically using SNMP traps, syslog events and similar. The network is generally the data master for this assurance-style data, so it makes sense to pull data from the network wherever possible (ie bottom-up data flows).
Fulfilment data, in the form of customer orders, network designs, etc are often captured in external systems first (ie as master) and pushed into the network as configurations (ie top-down data flows).
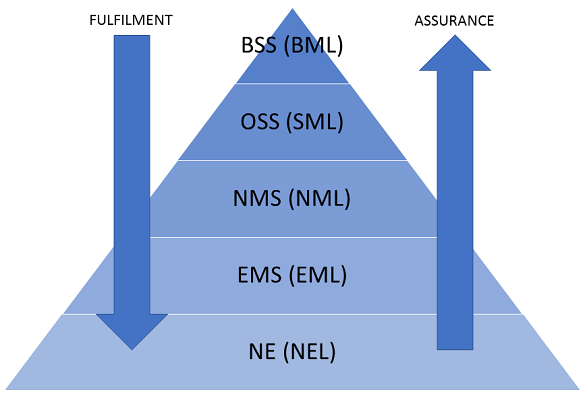
These two flows meet in the middle, as they both tend to rely on network inventory and/or resources. Bottom-up – Network faults to be tied to inventory / resource / topology information (eg fibre cuts, port failure, device failure, etc) which are important for fault identification (Root Cause Analysis [RCA]). Similarly for top-down – customer services / circuits / contracts tend to consume inventory, capacity and/or other resources.
Looking end-to-end and correlating network health (assurance) to customer service health (fulfilment) (eg as Service Level Agreement [SLA] analysis, Service Impact Analysis [SIA]) tends to only be possible due to reconciliation via inventory / resource data sets as linking keys.
Seeding an OSS with inventory / resource data can be done via three methods:
Options 1 and 2 are probably the more traditional method of initial seeding of OSS databases, mainly because they tend to be faster to demonstrate progress.
Option 3 is the front-loading option that can be challenging in the short-to-medium term but will hopefully prove beneficial in the longer term (just like knowledge transfer and automated testing).
It might seem easy to just suck data directly out of the network, but the devil is definitely in the detail, details such as:
The vexing question arises – do you front-load and seed via auto-discovery or perform a creation / migration that requires more manual intervention? In some cases, it could even be a combination of both as some domains are easier to auto-discover than others.
In the the last month or so 8 different carriers, from a variety of places around the planet, have reached out to us to discuss
Telco keeps worrying about a skills shortage. But a group of Solent University students just reminded me that the talent is still there. We just
Most OSS experts focus on the implementation and post-go-live performance aspects of a transformation. That makes perfect sense, because they’re the most visible phases. But

Everyone wants to know who the best OSS vendor is. But since there are 500+ OSS/BSS vendors, that question usually starts an argument, rather than